By: Frank Vesce
Chief Information Security Officer • Legal & Technology Risk Department
April 8, 2026
AI adoption in private markets is accelerating. From due diligence to investor reporting, firms are deploying AI tools to drive efficiency and competitive advantage. But alongside that acceleration comes a reality that many organizations still fail to confront: AI security is not a one-time implementation. It is a continuously evolving discipline, and the firms that treat it otherwise are already behind.
AI Security Is Not a One-Time Implementation
Traditional security models were built around relatively stable environments. You assessed, you remediated, you moved on. AI breaks that model entirely.
AI systems are inherently dynamic. Models are updated, fine-tuned, and retrained. Integrations multiply. User behaviors shift. The threat landscape evolves in parallel, with adversaries now actively experimenting with AI-driven attacks, including model manipulation and data poisoning.
Static controls fail in dynamic environments. A point-in-time security assessment tells you where you stood six months ago. It does not tell you where you stand today. For credit and private equity firms managing sensitive LP data, proprietary deal flow, and highly regulated financial activity, that gap is unacceptable.
The uncomfortable truth is you cannot avoid AI risk. Instead, you must govern it. This demands a fundamentally different approach: continuous AI security.
The Rise of Shadow AI in Private Markets
However, before firms can build a continuous security model, they must confront the risk already inside their walls: shadow AI.
Shadow AI refers to the unauthorized or unvetted use of AI tools by individuals or teams, without visibility or approval from IT, risk, or compliance functions. This is not hypothetical. It is happening now, across every tier of the organization, often with entirely good intentions.
In private markets, the stakes are particularly high. Consider the exposure scenarios:
- An analyst uses a consumer AI tool to summarize LP communications, inadvertently uploading confidential investor data to an unvetted third-party platform.
- A deal team feeds proprietary financial models into an AI assistant with no data residency controls or contractual protections.
- An operations team automates investor reporting using an AI tool that stores interaction data for model training.
Each of these scenarios can trigger regulatory exposure, breach confidentiality agreements, and undermine the fiduciary duty at the core of private markets operations. As global AI regulation takes shape, from the EU AI Act to emerging SEC guidance, the compliance risk of shadow AI will only increase.
Why Traditional Security Programs Break Down with AI
Most enterprise security programs were not designed for the pace or complexity of AI adoption. Three structural gaps consistently emerge:
- Periodic audits versus real-time risk. Annual or quarterly assessments cannot keep pace with continuous AI model changes and evolving threat vectors.
- Lack of visibility into AI usage.Without dedicated tooling, security teams have no reliable view of which AI platforms employees are accessing, what data is being shared, or where the perimeter actually lies.
- Decentralized experimentation. Business units are adopting AI tools independently, faster than governance structures can adapt, creating fragmented risk that is difficult to aggregate or remediate.
The result is a security program that looks comprehensive on paper but has significant blind spots in practice. Closing those blind spots requires a purpose-built framework.
The Continuous AI Security Model
The Continuous AI Security Model is a five-pillar operating framework designed specifically for the demands of AI-enabled private markets firms. It shifts security from a reactive function to a proactive, always-on capability.
1. Continuous Controls Monitoring (CCM)
Continuous Controls Monitoring provides real-time assessment of your cybersecurity controls. Not a snapshot, but a live read of whether your defenses are functioning as intended.
For AI environments, CCM means tracking authentication activity, monitoring data access patterns, validating encryption standards across AI integrations, and surfacing control failures as they occur. The shift from reactive to proactive is not incremental. It is categorical.
2. AI-Specific Scenario Testing
Tabletop exercises are not new to security teams. But most existing exercises were not designed for AI-specific threat scenarios. That gap needs to close.
Firms should regularly simulate AI-driven data exfiltration events, model manipulation or adversarial input attacks, and unauthorized AI tool usage that triggers regulatory exposure. These exercises do not just test response plans. They expose the gaps in those plans, enabling continuous improvement of both technical controls and human response protocols.
3. Embedded Risk and Business Alignment
Security cannot operate at arm’s length from the business units driving AI adoption. Embedding risk officers directly within deal teams, operations functions, and portfolio company leadership creates a frontline feedback loop that centralized security teams simply cannot replicate.
Risk officers surface emerging AI use cases in real time, flag control gaps before they become incidents, and help security decisions keep pace with operational velocity.
4. Continuous Testing and Validation
Penetration testing must extend explicitly to AI systems. This means assessing AI model endpoints, API security, data pipelines, and the third-party platforms on which AI tools depend.
The recent Base44 vulnerability, where unauthenticated API endpoints allowed attackers to bypass Single Sign-On (SSO) and gain unauthorized access across environments, illustrates exactly why AI infrastructure cannot be treated as implicitly trusted. Automated testing provides coverage at scale; manual testing uncovers the logic flaws that automation misses. Both are necessary.
5. Shadow AI Detection and Governance
Detection comes first. AI usage audits, Cloud Access Security Brokers (CASBs), and AI-specific Data Loss Prevention (DLP) tools provide the visibility needed to understand which AI platforms are actually in use across the organization and what data is flowing through them.
Governance follows. Establishing approved AI toolkits, clear usage guidelines, and AI governance frameworks aligned with existing cyber, legal, and compliance functions gives teams a structured path to AI adoption that does not require bypassing security controls to move fast.
Enabling Innovation Without Losing Control
The goal is not to restrict AI. It is to govern it so it can deliver to its full potential.
Private markets firms that approach AI security primarily as a constraint will lose talent, competitive edge, and operational momentum. Those that build AI governance as an enabler, making it straightforward for teams to adopt AI tools through approved, secure channels, will capture the productivity gains AI offers without accumulating the risk exposure that comes with ungoverned adoption.
Speed and security are not in opposition. Governance is what makes speed sustainable.
Governing the AI Ecosystem in Practice
In practice, enabling AI safely is not about restricting tools. It is about defining a governed ecosystem in which innovation can happen at speed without exposing the organization to unmanaged risk. As AI adoption accelerates, data no longer flows through a single system or vendor. It moves across large language models (LLMs), AI platforms, cloud providers and other ‘subprocessors’, and internal applications, often within a single workflow. Without clear guardrails, that complexity quickly becomes a source of uncontrolled exposure.
Forward-thinking firms address this by establishing an approved AI ecosystem: a defined set of vetted LLMs, AI platforms, subprocessors, and internally managed applications through which data is permitted to flow. This creates a controlled integration layer where teams can confidently build and deploy AI-driven workflows, knowing that each component has been assessed for security, contractual safeguards, and data handling practices. Just as importantly, it provides transparency into how data is processed and which third parties may be involved, reinforcing trust rather than undermining it.
This model does not eliminate flexibility. When new tools or capabilities are required, they are evaluated through a structured governance process that includes security, legal, and compliance functions. The result is not friction, but clarity: teams know how to move forward, and the business avoids the hidden risks of ad hoc adoption. In this way, governance becomes the mechanism that enables both speed and control. It ensures that innovation scales safely, data remains protected across every integration point, and AI adoption strengthens, rather than compromises, the firm’s security posture.
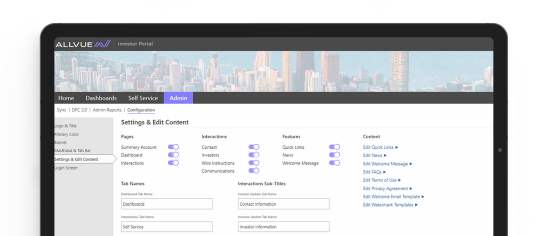
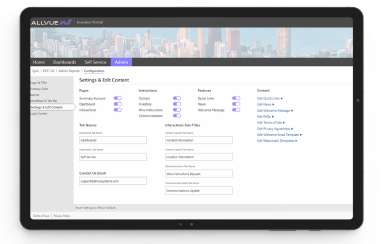
How Allvue Enables Continuous AI Security
Allvue’s AI solutions for private markets are built with Continuous AI Security in mind. We operationalize this governance model through a defined, policy-driven AI ecosystem. AI integrations are restricted to approved large language models, vetted subprocessors, and internally managed applications. Client data only flows through environments that meet strict security, legal, and compliance standards. Subprocessors are transparently documented and governed, with clear controls over how and where data may be processed.
When new AI tools or integrations are required, they are subject to formal cross-functional review across Information Security, Legal, and Compliance before being introduced into the environment. This approach allows Allvue to continuously expand its AI capabilities and develop new AI offerings while maintaining full control over data, reinforcing client trust, and ensuring that innovation never comes at the expense of security.
Rather than external or uncontrolled tools, Allvue delivers integrated AI capabilities designed for the data sensitivity and regulatory requirements of private capital markets firms. Key security capabilities include:
- Built-in monitoring and telemetry across AI interactions, providing the real-time visibility required for Continuous Controls Monitoring.
- Centralized AI governance so security, compliance, and legal teams maintain oversight of AI usage without creating bottlenecks for business operations.
- Role-based AI access controls ensuring that users interact only with AI capabilities appropriate to their function and data authorization level.
- Embedded AI by design. Allvue’s AI is integrated directly into front-to-back office workflows, eliminating the need for teams to seek external AI platforms to get their work done.
Continuous AI security is what turns AI from a risk into a competitive advantage. With the right architecture, governance, and operating model in place, private markets firms can move faster, innovate confidently, and protect the data that defines their business.
Learn More About Information Security and AI at Allvue
For more details on Allvue’s information security program, visit:
- The Allvue Trust Center, which details our security practices, compliance frameworks, and data protection standards.
Ready to start your AI journey with Allvue? Learn more about our secure AI platform.
More About The Author

Frank Vesce
Chief Information Security Officer • Legal & Technology Risk Department
Frank Vesce is a veteran cybersecurity leader with over 25 years of experience driving value across the financial, insurance, and tech-startup sectors including helping to scale a firm from funding through IPO. Currently the CISO at Allvue Systems, Frank previously spent a combined 20 years at Goldman Sachs in senior global leadership roles. An authoritative voice in the field, Frank is the author of The Pragmatic CISO, a guide designed to help businesses of all sizes navigate complex security landscapes and eliminate technology bloat. He serves as a Cybersecurity Advisor to the U.S. Coast Guard (NY/NJ), holds a Government Clearance, and has presented at Harvard, MIT, the FBI, and the NY Counter Terrorism Bureau. Beyond technology, Frank is a dedicated advocate for foster care and non-profits like Year-Up, having testified before Congress on the power of private-sector partnerships with organizations like Casey Foster Care.